Keycloak Integration
Kion integrates with Keycloak as a SAML 2.0 provider. This integration allows users to access Kion using familiar logins and consolidates user management.
This guide details both encrypted and unecrypted assertion options and was built against Keycloak v16.1.1.
Configuration
1. Obtaining Information from Kion
- Login to Kion as an administrator.
- Navigate to Users > Identity Management Systems.
- Click Add New.
- Select SAML 2.0 as the IDMS Type.
- Enter a name for the IDMS. Users see this name when selecting the IDMS on the Kion login page.
- Copy the following values to a text file. They will be used to configure Keycloak.
- Service Provider Issuer (Entity ID)
- Service Provider ACS URL
2. Obtaining Information from Keycloak
- On a separate browser tab, log in to Keycloak.
- Choose the Realm where you plan to install the Kion SSO Client. This defaults to the master realm.
- Navigate to Realm Settings.
- Click SAML 2.0 Identity Provider Metadata.
- Copy the Keycloak metadata to a text file. It will be used to configure Kion.
3. Configuring Kion
- Return to the new IDMS configuration you started to create in Kion.
- Paste the Keycloak metadata into the Identity Provider Metadata field.
- Locate and copy the entityID in the keycloak metadata. The format should follow
https://<YOUR-KEYCLOAK-URL>/auth/realm/<REALM-NAME>.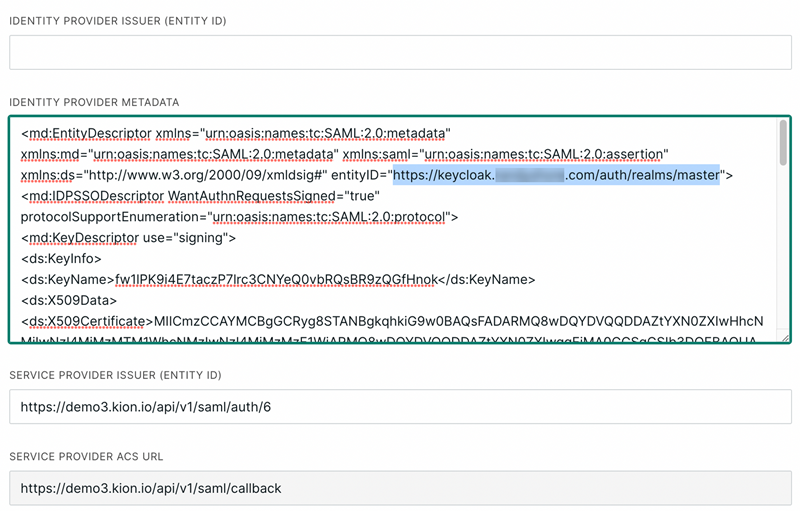
- Paste the entityID in the Identity Provider Issuer (Entitiy ID) field.
- In the Name ID Format field, enter
urn:oasis:names:tc:SAML:1.1:nameid-format:unspecified - For the Assertion Mapping First Name, enter
urn:oid:2.5.4.42 - For the Assertion Mapping Last Name, enter
urn:oid:2.5.4.4 - For the Assertion Mapping Email, enter
urn:oid:1.2.840.113549.1.9.1 - For the Assertion Mapping Username, enter
urn:oid:1.2.840.113549.1.9.1 - (Optional) Upload the Keycloak logo for the Service Provider Icon. Users see this image when selecting the IDMS on the Kion login page.
- Click Create IDMS.
- On the IDMS details page, click the ellipsis menu and select Download Metadata. This downloads the Kion metadata for configuring Keycloak.
4. Configuring Keycloak
- Return to Keycloak, ensuring you are in the same realm that you selected earlier.
- Navigate to Clients.
- Click Create.
- Import the Kion metadata file you downloaded earlier. This populates the Client ID and the Protocol Type (SAML).
- In the Client SAML Endpoint field, paste the Service Provider ACS URL you obtained from Kion.
- By default, this uses encrypted SAML assertions and the Kion service provider certificate is added automatically. If you prefer to use unencrypted assertions, disable the Encrypt Assertions option and delete the certificate from the Keys tab.
- Select the Settings tab.
- Disable the following options:
- Sign Assertions
- Client Signature Required
- Force Name ID Format
- Save your configuration.
Testing
- Open an incognito session in your browser.
- Go to the login page for your instance of Kion.
- Click the button for the Keycloak IDMS you just created.
- Authenticate with Keycloak to log in to Kion.
- By default, the built-in Keycloak administrator user doesn't have a first name, last name, or email address configured. We recommend either configuring those fields beforehand or using a different user in this test.
- In Kion, click the display name initials in the top-right corner, and select My Profile.
- Verify the first name, last name, email, and username are as expected.
(Optional) Editing Assertion Mappings
Assertion mappings are the names of the SAML assertions that Kion uses to populate user records. We recommend configuring the First Name, Last Name, Email, and Username fields to be more user friendly.
In Kion:
- Navigate to Users > Identity Management Systems.
- Click the ellipsis menu next to your Keycloak IDMS and select Edit IDMS.
- For the Assertion Mapping First Name, enter
givenName - For the Assertion Mapping Last Name, enter
surname - For the Assertion Mapping Email, enter
email - For the Assertion Mapping Username, enter
email - Click Save.
In Keycloak:
- Navigate to Clients.
- Select the configuration you created for Kion.
- Select the Mappers tab.
- Click Add Builtin.
- Select X500 email, role list, X500 givenName, and X500 Surname.
- Click Add Selected.
- Edit the SAML attribute name of the X500 givenName mapper to be
givenName. - Edit the SAML attribute name of the X500 Surname mapper to be
surname. - Edit the SAML attribute name of the X500 email mapper to be
email. - Save your changes.