Preventative Google Cloud IAM Roles
Kion uniquely offers the option to deny permissions on Google Cloud IAM roles. In Google Cloud, IAM permissions can be granted by IAM roles, but there is no way to deny permissions. We bridge this gap by enabling you to add denied permissions to IAM roles managed in Kion. You can deny specific permissions, or use wildcards to deny groups of permissions. Denials on IAM roles are inherited by descendant resources, enabling organization and department wide protections.
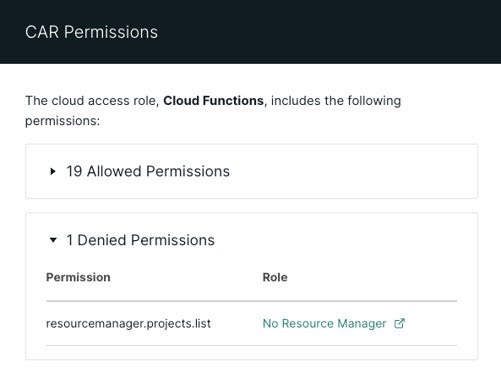
To see which permissions are allowed or denied on a cloud access role, navigate to the details page of a project with the role, select Cloud Management > Cloud Access Roles, click the ellipsis menu next to the role, and select View Permissions. This lists all permissions applied or denied by the role, including those inherited from parent resources.
Only permissions that can apply to projects are applied.
Fixing Common Federation Issues
Many of the Google provided IAM roles include permissions that can be applied to an organization or folder IAM policy but not to a project IAM policy. This can cause issues when federating into a Google Cloud project from Kion, since the federation process only updates the IAM policy for the selected project.
To help avoid federation errors, permission denials can prevent many of these organization/folder specific permissions from unintentionally being applied. If a Google Cloud IAM role with permission denials is added to a cloud rule and attached to a high-level OU, common errors can be prevented in any descendant cloud access roles.